A Chinese danger star, understood to have actually committed a series of state-sponsored espionage attacks, has actually been discreetly staging economically determined activities targeting the computer game market.
According to cybersecurity company FireEye, the cyber danger group– called Advanced Persistent Risk 41 (APT41) — is special because “it leverages non-public malware normally booked for espionage projects in what seems activity for individual gain.”
While the group appears to have actually been active a minimum of because 2012, the general public disclosure recommends that its twin inspirations emerged from 2014 onward.
Called Barium or Winnti by other business, APT41 has actually been formerly connected to numerous supply chain compromises targeting Asus, NetSarang, and CCleaner energy over the last few years.
Stabilizing espionage and economically determined attacks
APT41 is stated to have actually introduced a number of intelligence event projects ahead of important political occasions and tactical organisation choices, with concentrate on verticals like pharma, health care, retail, education, and virtual currencies.
The group has actually pursued business found in a minimum of 14 nations, consisting of France, India, Singapore, South Korea, the UK, and the United States, showing the international nature of the attacks.
In addition, it’s likewise regularly targeted the computer game market– advancement studios and publishers– straight and by means of supply chain compromises, even as the group moved far from taking copyright in 2015 following a historical Sino-US arrangement that put an end to cyber-enabled theft for commerical gain.
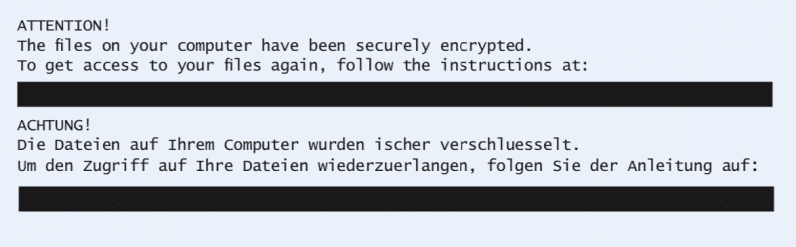
Per FireEye, the danger star tried to take information from a health care business while likewise concurrently releasing ransomware at a video game advancement studio.
The projects work by injecting malware into genuine computer game software application from third-parties, which are consequently dispersed to victim companies.
Moreover, APT41 has actually leveraged a range of techniques– spear-phishing, bootkits, recording server qualifications, and utilizing jeopardized digital certificates from video game studios to sign malware– in order to access to advancement environments and disperse harmful code.
Surprisingly, while the method operandi contaminated countless systems, the hackers eventually benefit from the invasion to target particular people, the scientists kept in mind.
When inside the environment, it makes use of tailor-made tools to get raised access to systems and create 10s of countless dollars in the video game’s virtual currency, which is probably offered in underground markets. Stopping working the goal, the group is likewise stated to have actually released ransomware to gather cash from the victim.
A do-it-all hacking group
What’s more, APT41 has actually shown to be something of a resourceful foe, acquiring abilities to take call record details from telecom business, and determine dissidents in China.
The findings come close on the heels of comparable disclosures by F-Secure and IBM, which have actually cautioned of increased malware attacks on banks, facilities, and state-run centers.
” APT41’s links to both underground markets and state-sponsored activity might suggest the group delights in defenses that allows it to perform its own for-profit activities, or authorities want to neglect them,” the scientists stated “These operations highlight a blurred line in between state power and criminal offense that lies at the heart of danger communities and is exhibited by APT41”
Check out next:
New Zealand greenlights Bitcoin income guideline– however it’s still a bad concept









